This talk will describe how the Windows Communication Foundation (Indigo) team applied the Trustworthy Computing Security Development Lifecycle to the WCF infrastructure. I’ll elaborate on the processes we followed for design reviews, threat modeling, and security testing. I’ll also describe how these processes (and lessons) can apply to securing your WCF applications
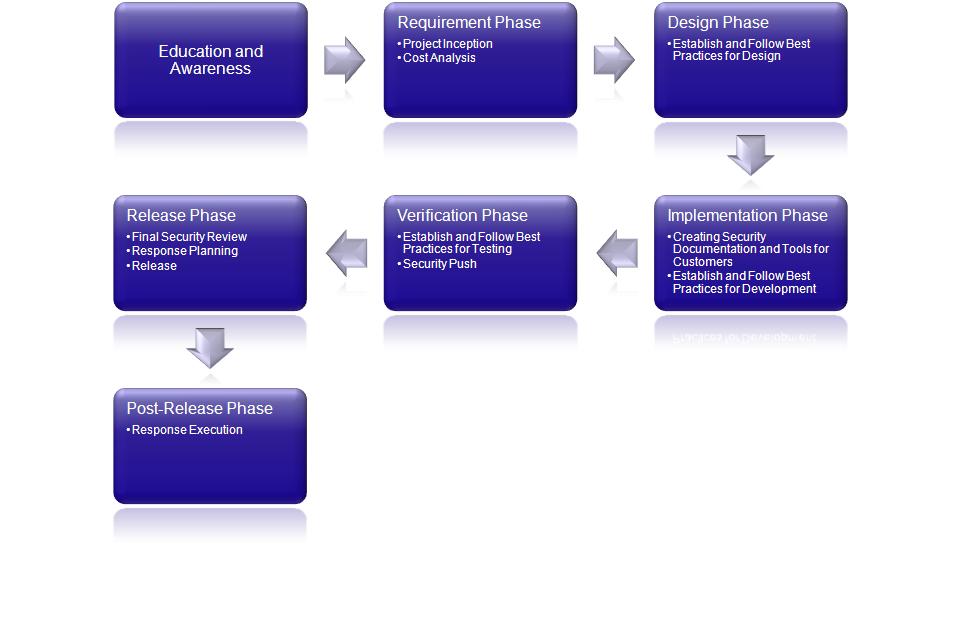
What is the SDL?
Process setup at Microsoft as a part of the TrustWorthy Computing effort.
Parallels standard software development lifecycle.
Focus on threat modeling and testing against threat model
Format: For each step of the process I will introduce the step, application to WCF, and how you can apply the process to your software.
Value
The SDL makes WCF secure.Apply SDL to your product
Secure by Design: the software should be architected, designed, and implemented so as to protect itself and the information it processes, and to resist attacks.
Secure by Default: in the real world, software will not achieve perfect security, so designers should assume that security flaws would be present. To minimize the harm that occurs when attackers target these remaining flaws, software's default state should promote security. For example, software should run with the least necessary privilege, and services and features that are not widely needed should be disabled by default or accessible only to a small population of users.
Secure in Deployment: Tools and guidance should accompany software to help end users and/or administrators use it securely. Additionally, updates should be easy to deploy.
Aucun commentaire:
Enregistrer un commentaire